About Me
I’m a cyber security student at Abertay University (Computer Science with Cyber Security) with an HND in Cyber Security from Dundee and Angus College, where I was awarded the Cyber Security Prize. I’m early in my career, but I take a structured, hands-on approach to learning and I’m serious about doing things properly.
Most of my development comes from practical work. I run a home lab using Kali Linux, Ubuntu, and Windows to practise web application testing, vulnerability assessment, basic network and wireless security, and secure configuration. I’m not interested in “tool collecting” or hype. I focus on understanding what a finding means, how it could realistically be abused, and how to fix it in a way that reduces risk.
I enjoy scripting and automation, mainly in Python, to make repeatable tasks faster and more consistent, especially around testing workflows and reporting. I also care about communication, because security work only helps if the results are understood and acted on. That’s one reason I’m interested in clear reporting and practical recommendations, not just technical output.
I’ve taken part in national cyber challenges including Cyber Leaders Challenge (BT Tower finals) and Cyber 9/12, and I regularly attend events such as SECURI-Tay and Hack Glasgow to stay connected to the community and keep my thinking grounded in real-world problems.
I’m now looking for opportunities where I can keep building practical experience in web application security, penetration testing, and security engineering, while contributing in a reliable, professional way.
Skills and Practical Experience
Kali Linux and Security Testing (Lab and Coursework)
I use Kali Linux in controlled lab environments to practise structured security testing and understand how common weaknesses are identified, verified, and communicated clearly.
Tools and activities:
- Nmap: host discovery and port/service scanning to map exposure and build an attack surface view.
- Nessus: vulnerability scanning to identify patching gaps and weak configurations in lab servers.
- Burp Suite: web request inspection and basic testing aligned to OWASP Top 10 concepts.
- Metasploit: used only on intentionally vulnerable systems (e.g., Metasploitable) to understand exploitation steps and typical indicators.
- Wireshark: packet capture for protocol understanding, troubleshooting, and spotting unexpected traffic.
- Snort: basic IDS setup to observe alerts and how activity appears in logs.
This work helped me link findings to real outcomes such as reducing exposed services, improving patching and configuration, strengthening web application behaviour, and understanding how attacks and detections look from both sides. All testing is done only in authorised environments.
Windows, Windows Server, and Microsoft 365 (Foundational)
I’ve built Microsoft-based lab environments to understand how typical business systems are structured and how core security controls are applied.
Tools and activities:
- Windows Server: configured roles such as DNS and DHCP in lab networks.
- Active Directory (AD): created users/groups and applied basic access controls and permissions.
- Group Policy (GPO): applied baseline settings to standardise and harden endpoints.
- Microsoft 365: regular use in work/study, with awareness of identity and access fundamentals.
Most real business risk comes from weak identity and access practices-too many privileged accounts, inconsistent configurations, and poor user lifecycle management. This foundation helps me understand where common weaknesses come from and how basic controls reduce risk.
Network Security and Firewall Fundamentals (Lab)
I’ve designed and tested small network setups in lab scenarios, focusing on practical controls that reduce attack surface and limit unnecessary access.
Tools and activities:
- Firewall rules: inbound/outbound controls using IPs, ports, and services.
- Exposure reduction: validating filtered/closed services through scanning and testing.
- Basic segmentation concepts: separating guest and internal access where supported.
- HTTPS/TLS basics: confirming secure access is enabled and unnecessary ports are restricted.
Good network security is mostly good decisions-only expose what is required, restrict management access, and keep internal services internal. These basics reduce common attack paths like exposed admin panels, accidental service exposure, and easy lateral movement.
Web Application Security (Foundational, Hands-on)
I’ve carried out structured web testing in university and lab environments to understand how common web weaknesses appear and how to report them clearly.
Tools and activities:
- Testing aligned with OWASP Top 10 concepts (authentication, access control, input handling, configuration).
- Basic vulnerability validation with evidence (requests, responses, screenshots) in controlled environments.
- Focus on fix thinking: input validation, least privilege, and safe configuration.
Web issues are a common entry point for real attacks. Practising this helps me identify practical risks (e.g., account abuse, data exposure, unsafe uploads) and communicate the fixes in a way that can actually be implemented, not just listed.
Wireless Network Security (Lab and Demonstrations)
I’ve built and secured wireless networks in lab and small-office style setups, focusing on secure configuration and understanding legacy weaknesses.
Tools and activities:
- Secure encryption configuration (e.g., WPA2/WPA3 in supported labs) and strong passphrases.
- Basic segmentation approaches for guest vs internal access where supported.
- Controlled testing of legacy weaknesses (e.g., WEP) to understand why insecure standards should not be used.
Wireless is often overlooked in small environments. Secure configuration and segmentation can prevent casual access, reduce risk from weak devices, and limit how far an attacker can move if a network is misconfigured.
Digital Forensics (Fundamentals)
I’ve used forensic tools in coursework and controlled practice to understand evidence handling, integrity, and basic artefact analysis.
Tools and activities:
- FTK Imager: forensic imaging of drives/USB media and integrity verification via hashes.
- Autopsy: review of files, browser artefacts, and basic timeline-style analysis from test images.
- Write-protection basics and documentation: following repeatable steps and avoiding changes to source data.
Even basic investigation work depends on doing things carefully and consistently. Understanding integrity and documentation reduces mistakes and helps ensure results are defensible.
Programming and Scripting (Security Support)
I use code to support learning, automation, and repeatable security tasks—mainly small tools and helper scripts.
Tools and activities:
- Python: basic automation (parsing, helper scripts, simple workflows to reduce repetitive tasks).
- C++ / Java: academic projects building understanding of programming and OOP.
- C# (Windows Forms): simple interfaces/tools for user interaction in coursework.
- HTML / CSS / JavaScript: basic web builds to understand how apps handle input and why security issues occur.
Being able to read and write code helps in security because it improves understanding of how systems fail and makes it easier to automate repeatable work. I don’t position myself as a full-time developer, but I can build and adapt practical tooling to support security tasks.
Legislation and Standards (Awareness)
I have a foundational understanding of key UK legislation and common security standards that guide ethical, legal, and responsible testing.
Key areas:
- UK GDPR and Data Protection Act (DPA)
- Computer Misuse Act
- ISO/IEC 27001 (conceptual awareness)
It keeps work responsible and scope-led: consent, authorisation, data minimisation, and clear documentation are part of good security practice, not optional extras.
Education
BSc (Hons) Computer Science with Cyber Security
Abertay University
September 2025 – Present
Focus on applied cyber security and secure software development, with particular emphasis on web application security, ethical hacking, and practical engineering skills.
Key areas of study:
- Web application security testing
- Software engineering practice
- Advanced ethical hacking concepts
- Computer networking (advanced)
- Fundamentals of machine learning
- Mathematics for cyber security
Higher National Diploma (HND) in Cyber Security
Dundee and Angus College
August 2024 – May 2025
Developed practical security skills across systems, networks, and defensive technologies, with strong emphasis on hands-on labs, structured testing, and clear reporting.
Key areas of study:
- Cyber security fundamentals and applied testing
- Intrusion prevention and monitoring
- Server administration for security
- Wireless device security
- Digital forensics fundamentals
- Object-oriented programming
- Social engineering and human risk
- Routing and network technologies
- Professional practice in cyber security
Higher National Certificate (HNC) in Cyber Security
Dundee and Angus College
August 2023 – May 2024
Graded Unit: Grade A
Built a solid technical foundation in cyber security concepts, networking, scripting, and ethical practice, supported by practical coursework and team-based projects.
Key areas of study:
- Ethical hacking and penetration testing fundamentals
- Data security and digital forensics
- Networking concepts and technologies
- Scripting for security tasks
- Computer architecture
- Professionalism and ethics in cyber security
- Internet of Things (IoT) security concepts
- Team working in computing
Certificate in Computer Technology with Cyber Security
Dundee and Angus College
August 2022 – May 2023
Introduced core IT and cyber security concepts, focusing on practical skills and foundational technical knowledge.
Key areas of study:
- Web development fundamentals
- Hardware and networking basics
- Introduction to Linux
- Ethical hacking awareness
- Computing project work
- Mathematics for computing
Projects / GitHub
My GitHub includes coursework and personal projects, mainly small scripts and programs built to support learning and practical security work. It’s a mix of automation, tooling, and exercises rather than polished commercial software.
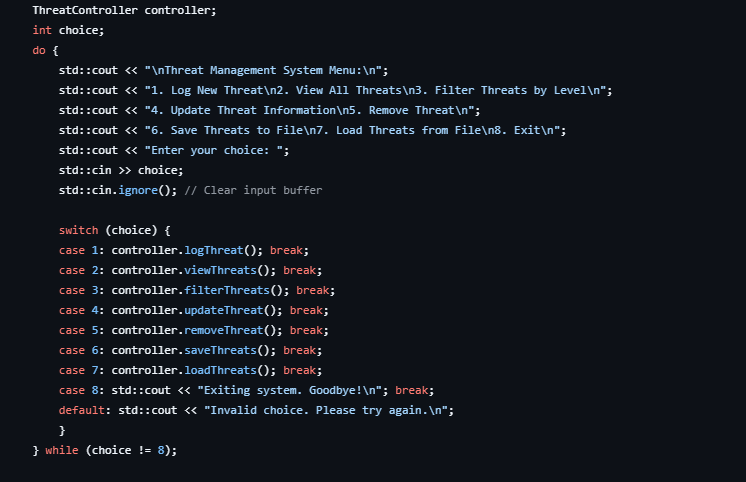
ThreatController (C++)
Menu-driven console app that simulates basic threat tracking. Create, view, update, filter, and save entries. Built for learning and portfolio use.
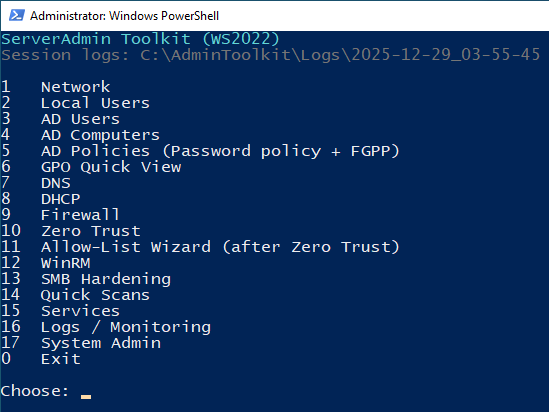
ServerAdmin Toolkit (PowerShell)
Menu-driven toolkit for common Windows Server admin tasks. Built to practise safe, consistent workflows in lab environments.
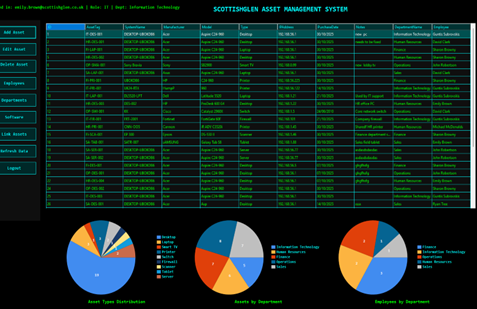
Asset Management System (C# / WinForms)
Coursework project demonstrating object-oriented design, role-based access, and database-backed asset tracking. Code available on request.
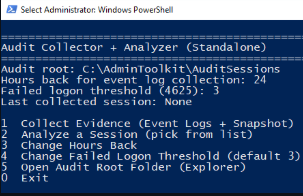
Windows Audit Collector (PowerShell)
Menu-driven tool that collects Windows logs and system evidence, then analyses sessions to highlight key security and admin events.
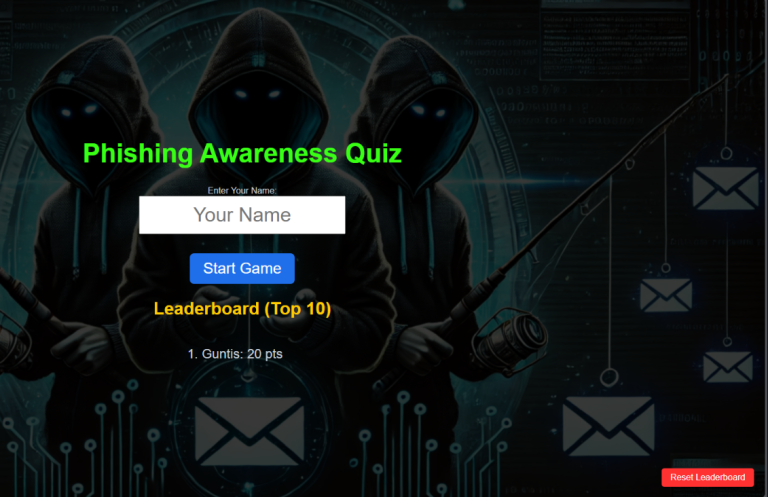
Phishing Awareness Game
Educational game designed to help users practise identifying common phishing emails and messages in a safe environment.
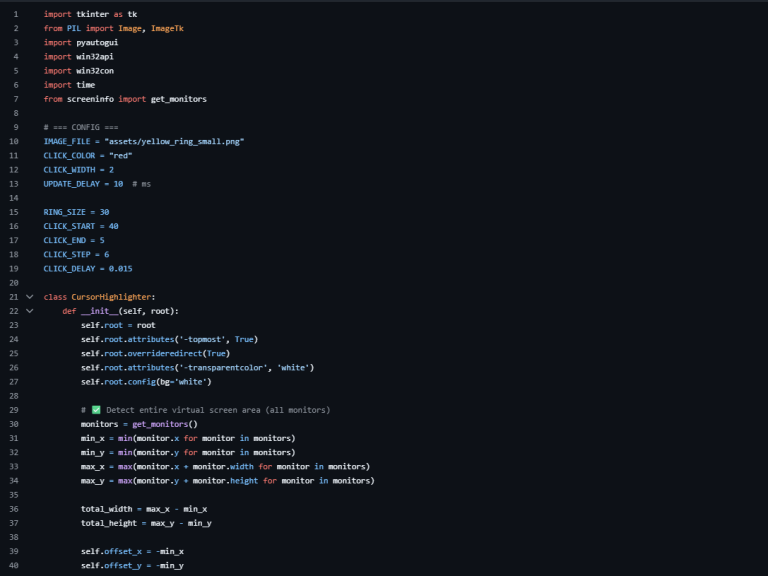
Cursor Highlighter (Windows)
Lightweight Windows overlay that improves cursor visibility during screen recordings, with a clear highlight and click indicator.
Work Experience
Supervisor - Ravensby Glass Manufacturing
June 2019 - August 2022
In this role, I learned how to lead a small team in a busy production environment where deadlines, quality, and safety all mattered. I was responsible for organising daily work, supporting staff, and keeping production running smoothly.
I regularly dealt with operational and technical issues, which meant learning new equipment and software used in production systems and resolving problems quickly and methodically. This role taught me to stay calm under pressure, follow process, document issues clearly, and take responsibility for decisions.
Key areas developed
- Team leadership and coordination
- Practical problem-solving
- Working with production systems and software
- Time management under pressure
Van Driver - Wing Fung Ltd. (Cash & Carry)
August 2015 - June 2019
In this role, I learned the importance of reliability, communication, and working independently. I interacted directly with customers, handled deliveries, and resolved issues as they arose during the day.
I was trusted with orders, payments, and customer information, which reinforced the need for accuracy, professionalism, and care when handling business-sensitive data.
Key areas developed
- Customer communication
- Independent working
- Reliability and time management
- Handling sensitive business information
Contact Me
Your next great hire might be just a click away!